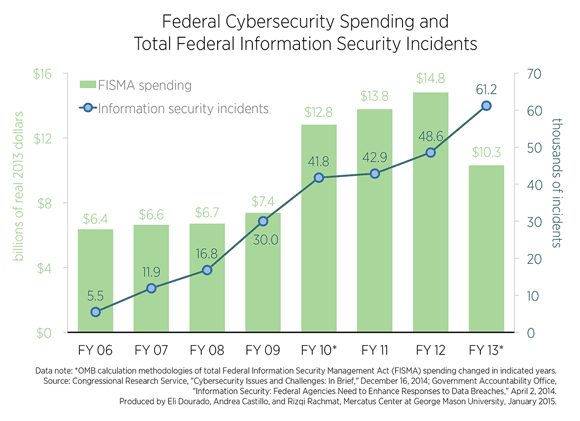
Cybersecurity for the New Frontier: Reforming the Federal Information Security Management Act - YouTube
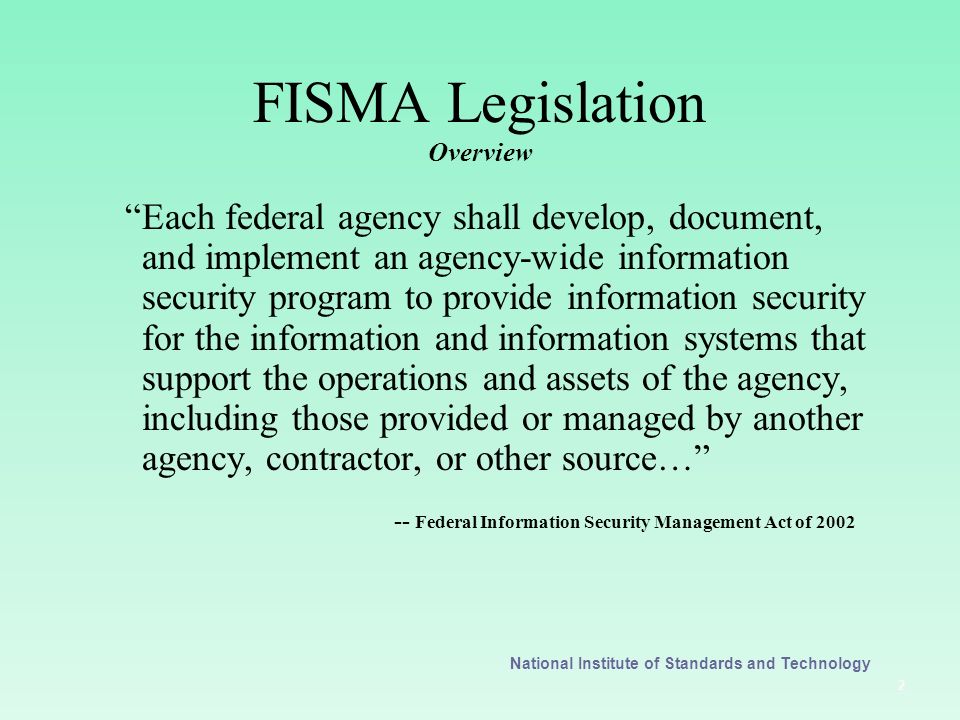
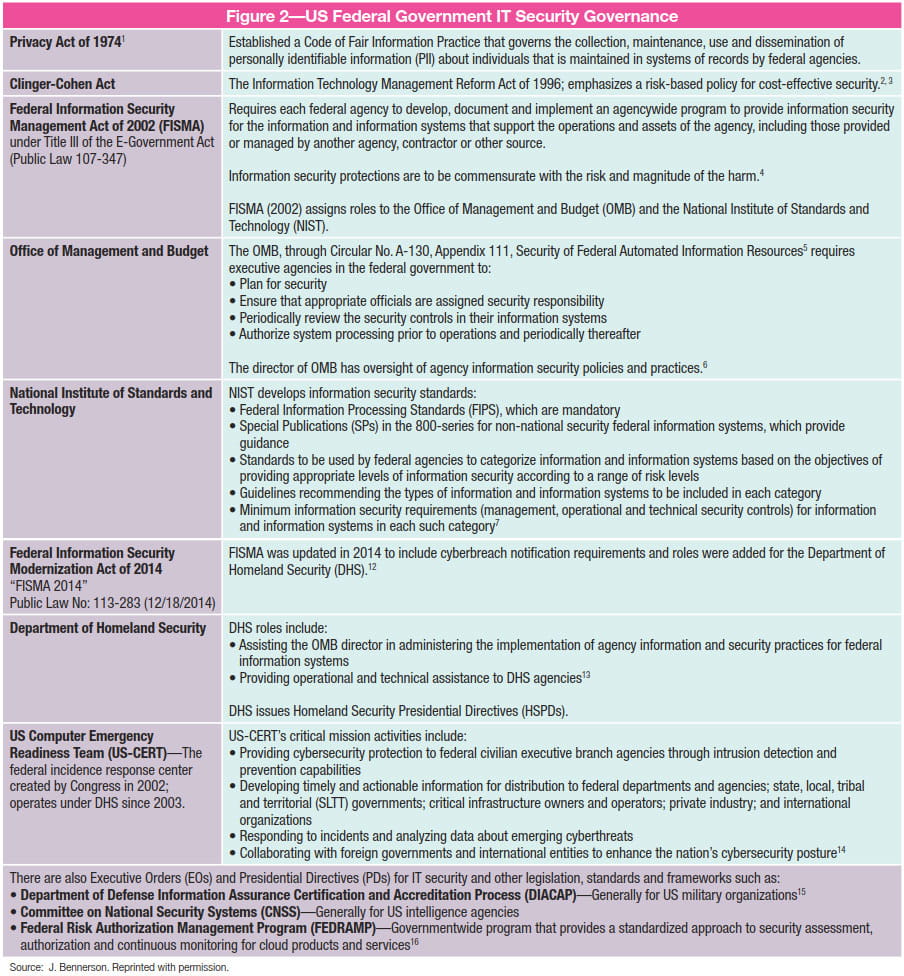
Federal Information Security Management Act (FISMA) By K. Brenner OCIO Internship Summer ppt download
Federal Information Security Management Act Applying NIST Information Security Standards and Guidelines Presented to the State of California April. - ppt download